Welcome back my fellow Hacking Enthusiasts. After looking at Information Gathering with Metasploit: Shodan in last weeks article, we are going to look at the Wayback Machine today. The Wayback Machine, or Internet Archive, is a long established website that collects snapshots from websites as they were in the past.
Now let’s first have a look at their website, so you get a better understanding of what I am talking about.
Table of Contents
- The Way Back Machine on the Web
- Information Gathering with Metasploit: The Wayback Module
- Conclusion
The Way Back Machine on the Web
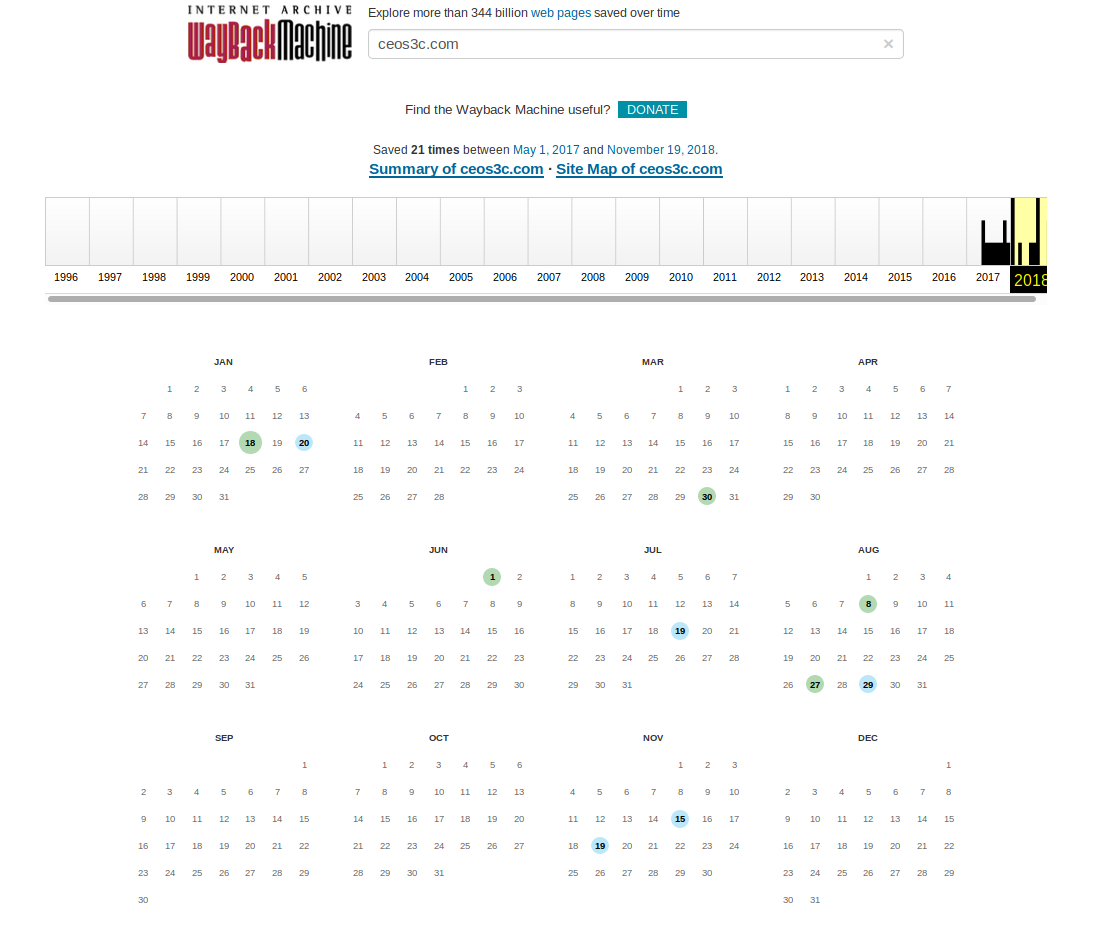
Just head to their website and enter any website that you want to check. For this, I use our own platform ceos3c.com
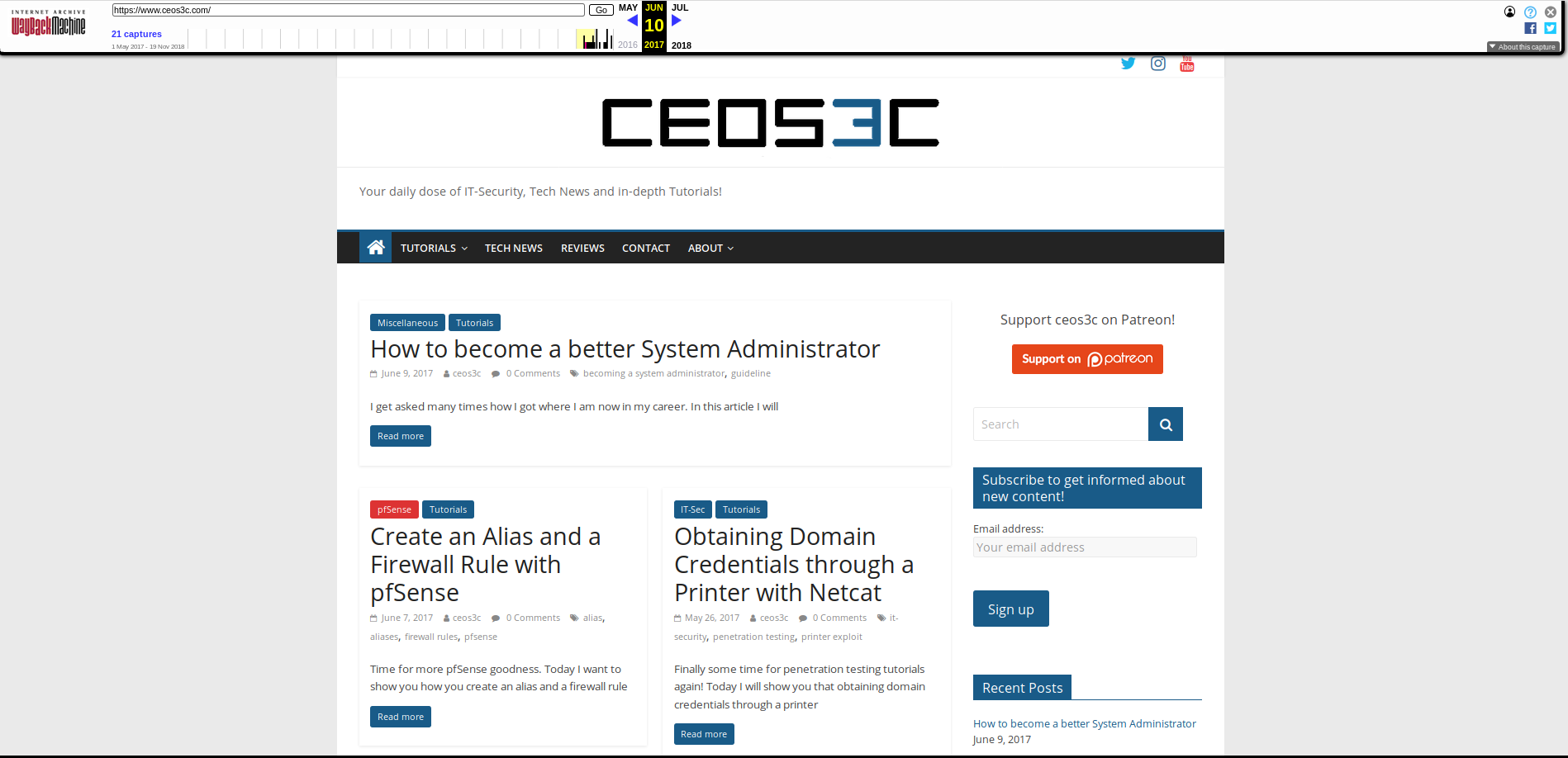
As you can see, there are several Snapshots. I think it started taking Snapshots of my site once it got a certain amount of traffic because it’s existing longer than since May 2017. Now if we click on an earlier date, say 10. Juli 2017, we get a copy of the website from that time. It can be a bit slow but look at that.
Boom, still rocking the old logo there. You can navigate through the website as if it was live, seeing all the dated information.
So, what is all that information good for you might ask? Some of you might have guessed it already, but this can be turned into a valuable asset for Social Engineering. On top, as I said in the previous article, the more information you have on a target, the better your chances are to breach their system.
The advantage of collecting information this way is, that because you don’t pull data from their Live Website, it is theoretically not detectable. There are cases where images might be pulled from the live website if you click on certain links, but the chance of being detected is way lower than running a scan against their Live Website.
Collecting this kind of information, especially the history of the company and some background knowledge, can give you a big advantage when preparing a Social Engineering Attack.
Information Gathering with Metasploit: The Wayback Module
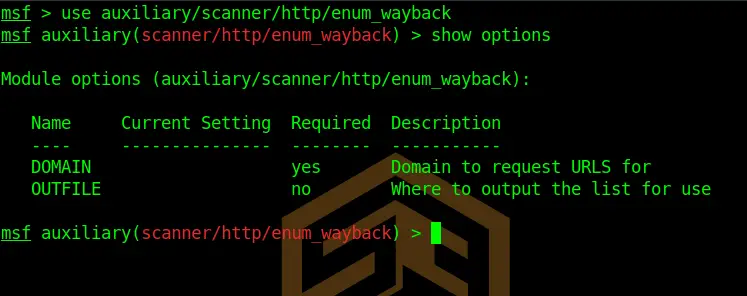
Our old friend Metasploit comes equipped with just the right tools for gathering this information on a larger scale: The enum_wayback module. Let’s fire it up in Metasploit.
msfconsole
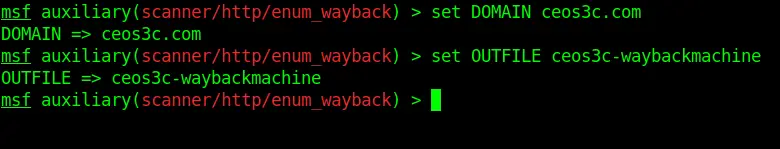
use auxiliary/scanner/http/enum_waybackCode language: PHP (php)You see we have to options that we can set; one is required one is not.
We have to set a Domain and we CAN set an Outfile, which I highly recommend for further processing. You probably wouldn’t want to read through hundreds of pages in your terminal window. So, let’s quickly do that.
set DOMAIN ceos3c.com
set OUTFILECode language: JavaScript (javascript)Running the Exploit
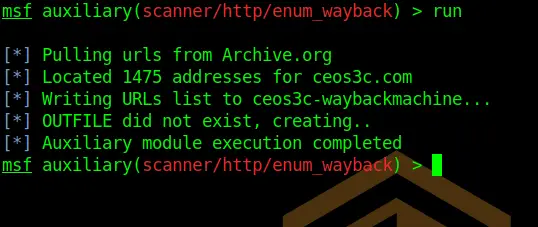
Time to run our Exploit.
runGreat, that seems to have been successful. The OUTFILE is located in your root directory.
Listing OUTFILE Contents
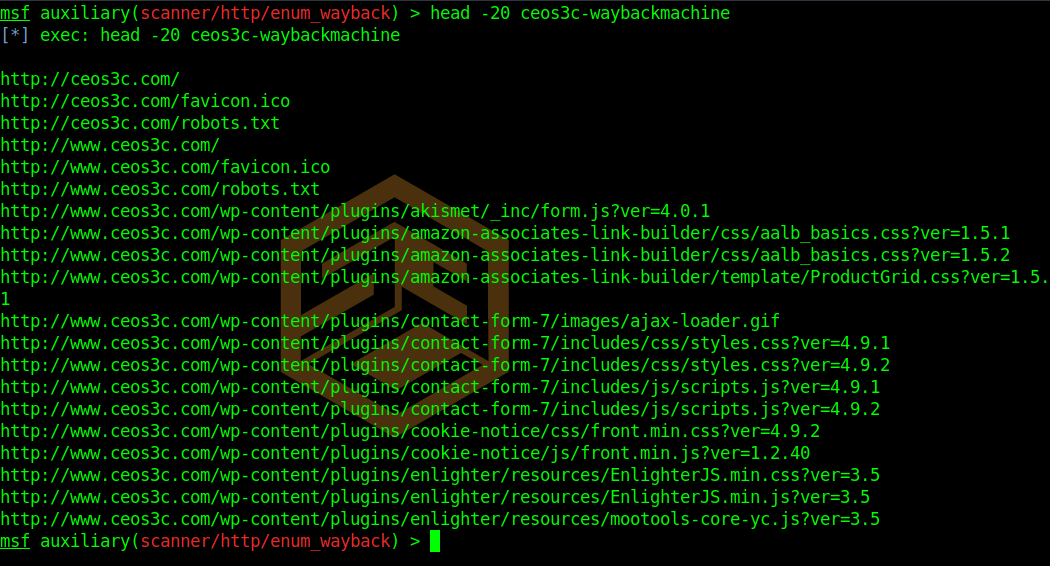
To check if there are actual URL’s in the OUTFILE you saved, you can check that by printing the first 20 lines using the following syntax.
head -20 ceos3c-waybackmachineFurther processing
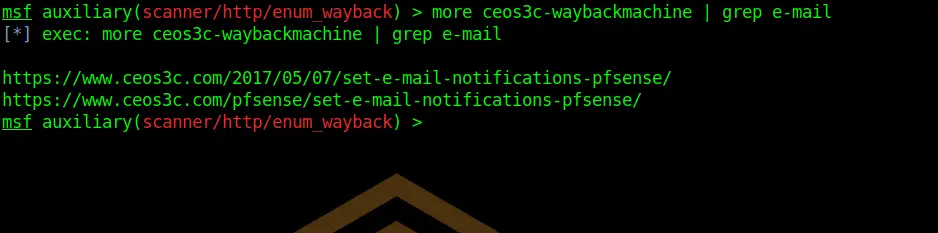
You can now either import this file to BurpSuite for further processing or, for a quick analysis simply utilize the grep command.
more ceos3c-waybackmachine | grep e-mailNaturally, I don’t store any email addresses on my website, but most companies do. So you could replace e-mail with anything like “Address” “CTO” “Audit” “Phone” or whatever might be of interest for you.
Conclusion
The Wayback Machine can be a really useful asset when composing a Social Engineering Attack, valuable information might be pulled from the past. It is not seldom to find the telephone number of a CEO or someone important back from the time when they haven’t been that relevant.
This is another Information Gathering with Metasploit method that you can add to your repertoire.