After a longer break I have finally decided to get back to doing some bounties, and I am really excited for that. First, I needed a break. Second, I was heavily invested in Web Development and have learned a ton in that sector. There is a lot of interesting stuff I have in my pipeline that will be very interesting for all of you Bug Hunters. Instead of just jumping in again, I decided to take a learning path on TryHackMe. Web Fundamentals to be concrete. I already know most of the stuff in there, but it can never harm to re-connect those synapses. As I have just started a day ago and it’s already Friday, there is not too much to share this week. I basically have just learned about how cookies work and thought I share.
What are Cookies exactly?
I’m just going to save you from a stupid cookie joke at this point. Cookies generally have a large number of uses. In most cases, they are used for session management and advertising (tracking cookies).
Why we use Cookies?
HTTP is stateless. That means, we need Cookies to keep track of things. Those things include but are not limited to:
Items in a shopping cart, who you are, what you have done on the website so far, authentication information, etc.
Cookie Properties
Cookies have certain properties, see below.
- A name
- To identify the cookie
- A value
- That’s where data is stored
- An expiration date
- When the browser get’s rid of the cookie (ex. 30 days)
- Path
- That determines what requests cookies will be sent with
Cookies are typically set in the response headers by the server with (“Set-Cookie”), but they can also bet set from JavaScript.
When you log into a website, you are given a session token. This token allows the server to differentiate your requests from another user’s. As you probably know, cookies can be stolen to impersonate someone else.
Manipulating Cookies
To understand how cookies work, we need to know how to manipulate them. There are a gazillion way to manipulate cookies, let me quickly show you two. In this example I use Adam Langley’s excellent CTFChallenge.co.uk website.
Using Developer Tools
In Chrome, you can just press F12 and go to Application and select Cookies in the left pane. In FireFox it is also F12 and then you find the Cookies within the Storage tab.
Here, I could just double-click inside of the Cookie string, change it, and send the request again with another cookie.
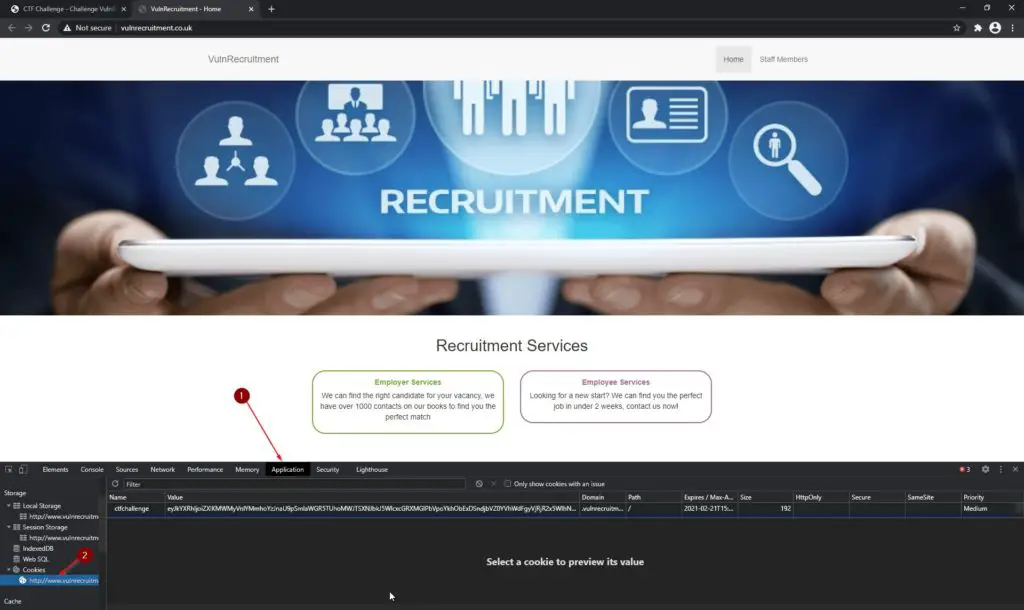
To be able to access VULNLTD’s site, you have to be logged in to Adam’s CTFChallenge.co.uk.
Hence, if I open the same website inside of a incognito window, I am not able to access the site, due the lack of the cookie:
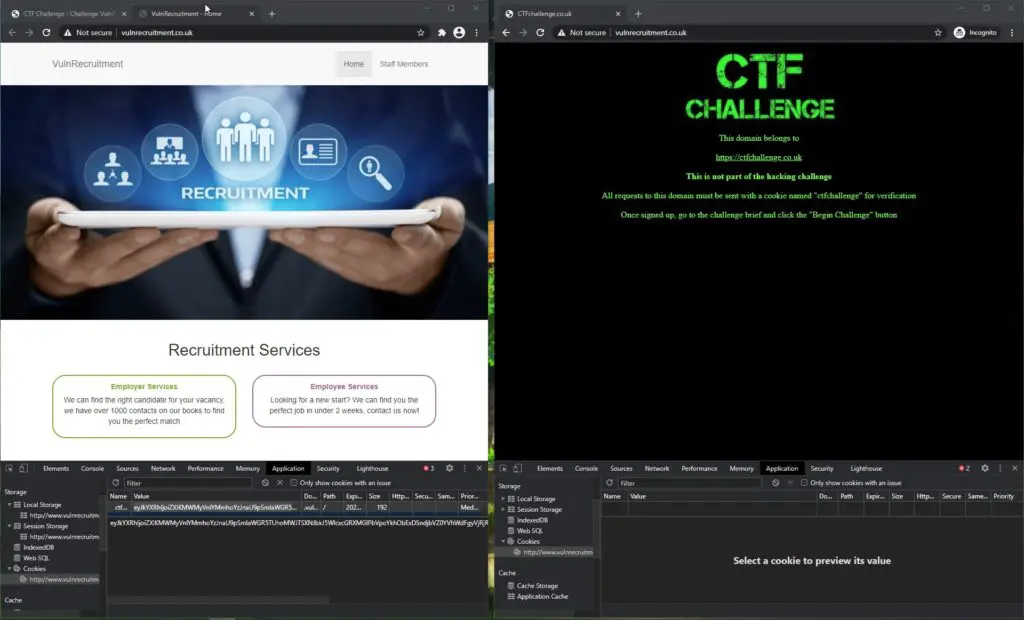
If I now go ahead and copy the cookie from the left window (the logged in session) to the right, unauthenticated window and hit F5 to refresh:
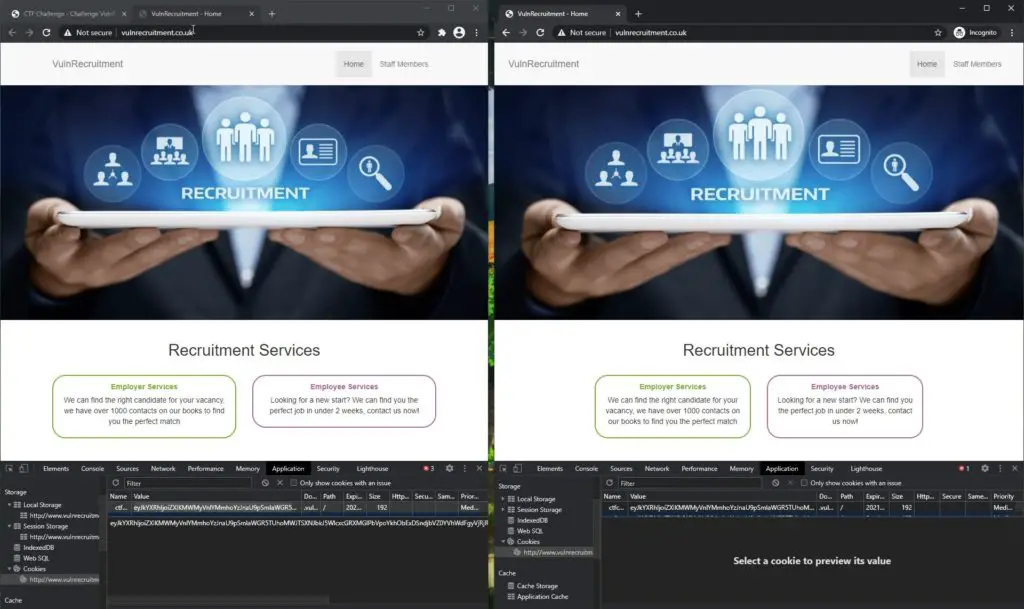
Voila, we are in. You get the gist of it I guess?
Using Curl
We can also use Curl with cookies. To do that, we need the name of the cookie and it’s value. We know which is which by simply looking at the tab in dev tools.
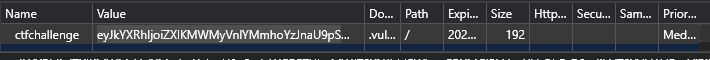
Let’s try to send a GET request to Adam’s challenge without being authenticated.
curl <http://www.vulnrecruitment.co.uk/>
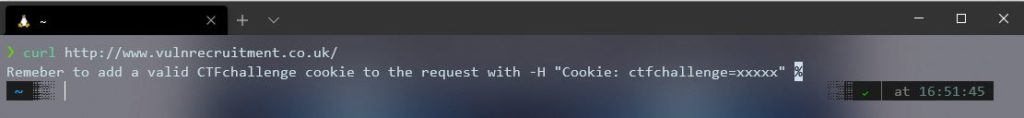
Huh, didn’t work? Of course not! But Adam gives us a hint. Let’s try that again:
curl -H "Cookie: ctfchallenge=MyCookie" <http://www.vulnrecruitment.co.uk/>
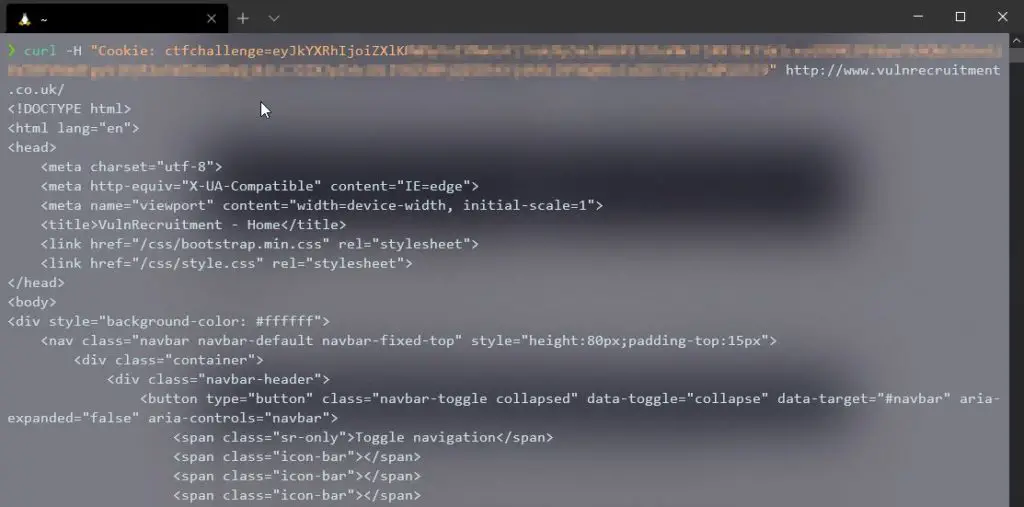
Awesome! Now we also know that Adam doesn’t like to write CSS and uses Bootstrap. I think that should get the point across.
Other tools to modify and send cookies with
- Burp Suite
- Postman
- Curl
- Browser Dev Tools
- Probably tons of other tools
Now you should know how cookies work.
Conclusion
Ah, writing that was fun! I am excited to get back to this after taking a break. I think if you are a Bug Bounty beginner, now is the right time to jump in, as I start from the beginning again as well. Those posts will be weekly on Fridays.
Check out older episodes of The Bug Bounty Diaries here.
The Best Way to stay Up-to-Date with my Content
- Sign up for the Newsletter
- Bookmark my LinkTree
- Follow me on Twitter
- Subscribe to me on YouTube
- Become a Patron and join the Members Only Discord Channel


Hey bro. I’m from india and I’m a new subscriber. I really love your content and the time and effort yu r sharing. It would be much helpful if you reply to my question. I’m a noob from non tech background just finished bcom. I do not know programming or networking. I want to be a blockchain developer which will be my stable profession and also interested in ethical hacking. I do not know how or from where do I start. Should I learn front end web development first? I want tolearn both hacking and blockchain simultaneously please help me brother. Thank u🙏❤
Thank you brother, appreciate it!